[ad_1]
Apple
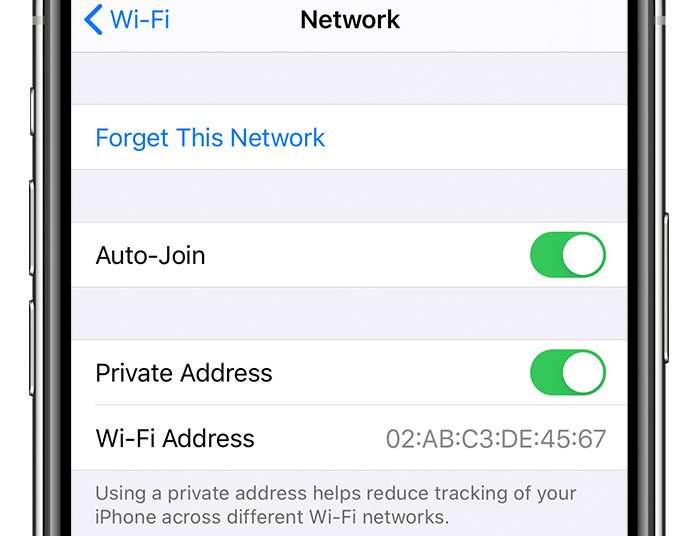
Three years in the past, Apple launched a privacy-enhancing function that hid the Wi-Fi tackle of iPhones and iPads after they joined a community. On Wednesday, the world discovered that the function has by no means labored as marketed. Regardless of guarantees that this never-changing tackle can be hidden and changed with a personal one which was distinctive to every SSID, Apple units have continued to show the true one, which in flip bought broadcast to each different linked gadget on the community.
The issue is {that a} Wi-Fi media entry management tackle—usually referred to as a media entry management tackle or just a MAC—can be utilized to trace people from community to community, in a lot the best way a license plate quantity can be utilized to trace a automobile because it strikes round a metropolis. Living proof: In 2013, a researcher unveiled a proof-of-concept gadget that logged the MAC of all units it got here into contact with. The thought was to distribute plenty of them all through a neighborhood or metropolis and construct a profile of iPhone customers, together with the social media websites they visited and the numerous areas they visited every day.
Within the decade since, HTTPS-encrypted communications have turn out to be customary, so the flexibility of individuals on the identical community to watch different individuals’s visitors is mostly not possible. Nonetheless, a everlasting MAC offers loads of trackability, even now.
As I wrote at the time:
Enter CreepyDOL, a low-cost, distributed community of Wi-Fi sensors that stalks individuals as they transfer about neighborhoods and even complete cities. At 4.5 inches by 3.5 inches by 1.25 inches, every node is sufficiently small to be slipped right into a wall socket on the close by gymnasium, cafe, or break room. And with the flexibility for every one to share the Web visitors it collects with each different node, the system can assemble an in depth file of private information, together with the schedules, e-mail addresses, private pictures, and present or previous whereabouts of the particular person or individuals it displays.
In 2020, Apple launched iOS 14 with a function that, by default, hid Wi-Fi MACs when units linked to a community. As a substitute, the gadget displayed what Apple referred to as a “non-public Wi-Fi tackle” that was completely different for every SSID. Over time, Apple has enhanced the function, for example, by permitting customers to assign a brand new non-public Wi-Fi tackle for a given SSID.
On Wednesday, Apple released iOS 17.1. Among the many varied fixes was a patch for a vulnerability, tracked as CVE-2023-42846, which prevented the privateness function from working. Tommy Mysk, one of many two safety researchers Apple credited with discovering and reporting the vulnerability (Talal Haj Bakry was the opposite), instructed Ars that he examined all latest iOS releases and located the flaw dates again to model 14, launched in September 2020.
“From the get-go, this function was ineffective due to this bug,” he stated. “We could not cease the units from sending these discovery requests, even with a VPN. Even within the Lockdown Mode.”
When an iPhone or some other gadget joins a community, it triggers a multicast message that’s despatched to all different units on the community. By necessity, this message should embrace a MAC. Starting with iOS 14, this worth was, by default, completely different for every SSID.
To the informal observer, the function appeared to work as marketed. The “supply” listed within the request was the non-public Wi-Fi tackle. Digging in somewhat additional, nonetheless, it turned clear that the true, everlasting MAC was nonetheless broadcast to all different linked units, simply in a unique subject of the request.
Mysk printed a brief video exhibiting a Mac utilizing the Wireshark packet sniffer to watch visitors on the native community the Mac is linked to. When an iPhone working iOS previous to model 17.1 joins, it shares its actual Wi-Fi MAC on port 5353/UDP.
Improve to iOS 17.1 to stop your iPhone from being tracked throughout Wi-Fi networks.
In equity to Apple, the function wasn’t ineffective, as a result of it did stop passive sniffing by units such because the above-referended CreepyDOL. However the failure to take away the true MAC from the port 5353/UDP nonetheless meant that anybody linked to a community might pull the distinctive identifier with no hassle.
The fallout for many iPhone and iPad customers is prone to be minimal, if in any respect. However for individuals with strict privateness menace fashions, the failure of those units to cover actual MACs for 3 years might be an actual downside, significantly given Apple’s specific promise that utilizing the function “helps cut back monitoring of your iPhone throughout completely different Wi-Fi networks.”
Apple hasn’t defined how a failure as fundamental as this one escaped discover for thus lengthy. The advisory the corporate issued Wednesday stated solely that the repair labored by “eradicating the susceptible code.”
This put up has been up to date so as to add paragraphs 3 and 11 to supply extra context.
[ad_2]